Altus Security & Trust
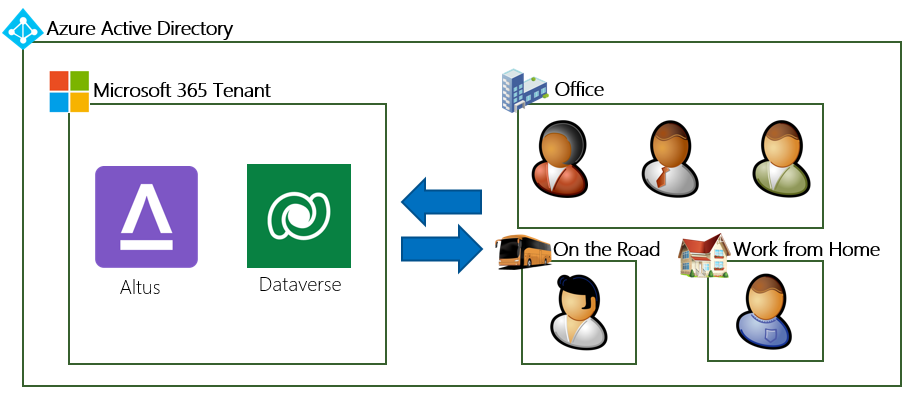
From a security perspective Altus is deployed as a Power App into your own Power Platform Dataverse environment. From this location, data is stored, transmitted and processed within your own M365 tenancy governed by your own security policies and that of Azure Active Directory.
While Altus does supply regular updates to the software and static assets from external locations, the processing, storage and transmission of customer data occurs within the organisation. This allows Altus to operate in organisations with conservative risk postures where solutions from traditional SaaS vendors would not be suitable.
Security Testing and Auditing
Penetration Testing is often a standard check box on many security questionnaires however in the case of Altus the security perimeter for Authentication and Authorisation is the Azure AD service itself with access to customer data controlled by the Power Platform role based access controls. Funding penetration testing of the Microsoft products beyond the existing comprehensive testing performed by Microsoft would not provide an increased level of risk assurance, so we have instead chosen to focus on other certification efforts to further elevate risk transparency.
Altus takes compliance assurance seriously, and the product has been architected with a focus on trust and security. ISO 27001 Certification and SOC Type 2 Auditing are essential mechanisms for organizations to maintain robust security and risk controls, and Altus already has controls aligned with ISO 27001 standards and industry best practices.
It's important to note that Altus doesn't operate any equipment that transmits, processes, or stores customer data. As a result, traditional certification and auditing activities may not significantly contribute to assessing the risk associated with the Altus product. Instead, we invite you to explore our platform certifications, which ensure the security and trustworthiness of the environment in which the Altus product operates. These certifications can be found at the Microsoft Security & Trust Center, reinforcing our commitment to providing a secure and reliable experience
Infrastructure Security
Datacentres used by the Altus product are the same as the customer M365 tenancy, managed and operated by Microsoft from within Azure. These datacentres comply with key industry standards, such as ISO/IEC 27001:2013 and NIST SP 800-53 and 800-88, for security and reliability. Operation within the M365 tenancy grants Altus the same high availability characteristics as native M365 services.
Multi-tenancy separation is ensured by way of each customer running their own instance of Altus within their tenancy and within a Power Platform environment boundary. Secure separation between multiple Altus instances in the one tenancy is easily achievable using Power Platform Environment containers.
Software Development Lifecycle
Code reviews are utilised to ensure that multiple members of our development staff review all code that goes into the product. An audit history is attached to every line indicating the author identity and who reviewed it. Staff are briefed to ensure the OWASP Top 10 and CVEs are addressed prior to approval.
Testing is performed by our QA team to test for functional, performance and security issues both in new additions to the product and via automated regression testing of the entire product every day. The automated testing suite used to perform these tests is available on request for customers who need to run these tests on their own customised version of the system to ensure customisations have not negatively affected standard functionality.
Static Code Analysis is a set of tools used during development to assist in finding errors and security problems in product. While these tools such as ESLINT are already in use in the Altus development process, we are moving towards a unified set of rules for the entire product which will provide increased levels of risk assurance.
Encryption
In transit: during the operation of Altus, data is transferred between the Client and Server via the well known HTTPS / TLS protocol. The version of TLS 1.2 is required and the product will not function on client devices that do not support it.
At rest: customer data is stored solely within the Microsoft Dataverse service within the customers own M365 tenancy. No external data stores are necessary. The Microsoft Dataverse service is very secure and is thoroughly tested and certified by Microsoft.
Privacy
Access to customer environments is needed by your deployment partner during the installation and configuration of Altus, but can be disabled prior to the transition to storing production and or sensitive information in the system.
GDPR and Australian Privacy Act can be relevant to Altus if it is extended to store personal information for EU or Australian citizens. Please seek legal advice relevant to your country of jurisdiction before using extending Altus to store personal information.
Data Breaches or other events requiring Incident Management are handled via a shared process model with Microsoft detailed in the Information Security Policy
IRAP assessments are an additional compliance check administered by the Australian Signals Directorate for SECRET use or below. The platform in which Altus operates has already been comprehensively assessed and IRAP attestations are available. While Altus doesn't operate any equipment that transmits, processes, or stores customer data we can cooperate IRAP assessors on request.